Little Known Questions About Third Eye Installation Systems London.
Such use CCTV technology has sustained privacy concerns in many parts of the globe, especially in those areas in the UK as well as Europe where it has actually become a routine part of police procedure.
You run a local business on Main Road. There is lots of foot traffic, particularly at weird hrs of the night. You can not rest and also activate the news at 3 am. The support states a "breaking as well as getting in" from looters at your store. You can not think your eyes, your heart sinks.
Third Eye Installation Systems for Beginners
In this overview, we will cover all you need to understand about CCTV. CCTV stands for Closed Circuit Television. Unlike conventional tv, CCTV is a closed-loop system where everything being transmitted stays in-house.
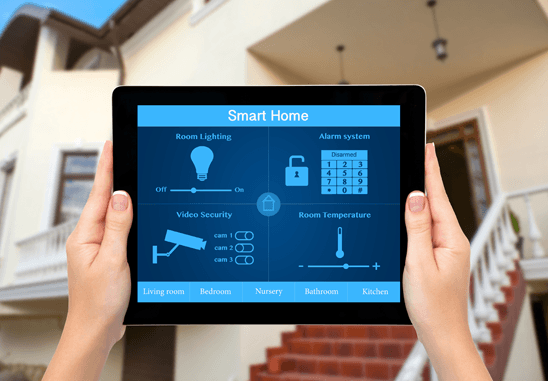
The main usage situation for CCTV is for safety objectives. Many businesses, bars, schools, dining establishments, banks, country clubs, and houses rely upon CCTV for defense. While the safety and security system may not quit the poor man, it will certainly stop criminal task to take place to begin with. Live footage was the main feature for CCTV when it initially stood out onto the safety and security scene.
Numerous houses make use of a protection video camera to make sure the safety of their enjoyed ones. Setting up an electronic camera on the outside of your home in several ways can significantly decrease the chances of something negative happening.
How Third Eye Installation Systems Cctv Installation can Save You Time, Stress, and Money.
The objective here is to extend footage of undesirable burglars. If you ever have strangers doing work with your house or have a sitter, a safety and security electronic camera is necessary for safeguarding your home when you're not about. Since we know what CCTV is, we can now ask just how alarm specialist does CCTV work? We need to be aware of the two types of protection electronic camera systemsanalog and also digital (IP).
The system itself is a bit more involved and also expensive, navigate to this website but well worth it in the end. This improves our protection process, as the camera takes the place of the DVR.

Not known Facts About Third Eye Installation Systems Intercom Intercom Systems
Your home and/or organization will certainly stay safe. No much longer will you need to ask what is CCTV and also how does it function. To learn all things protection with video monitoringread our blog today!.
This would certainly be especially beneficial for huge properties or one that holds useful equipment, products or info. As tape-recording video clip footage, a CCTV system can also inform you if there is task or motion on a certain electronic camera at an established time. For example, in the dead of evening whilst the company properties in closed and also staff members have actually gone house (Third Eye Installation Systems cctv installation).
A CCTV system can be made use of for the security of on-site activity, during as well as out of functioning hours, it can additionally be used to aid determine wanted bad guys, as well as act as a deterrent to prospective burglars. Would like to know the ins and outs of how a CCTV system functions? It's not complicated, but it does differ depending on the kind of system you install as well as the components made use of.
Some Known Questions About Third Eye Installation Systems Intercom Intercom Systems.
As stated previously, there are numerous types of CCTV systems with various cameras that have a raspberry pi 3 home automation variety of uses, such as evening vision, thermal imaging and also number plate acknowledgment. Both primary sorts of system are: Video cameras and also the remainder of the system is hard wired. Wireless No cables are needed as the system functions using a net connection.
Varifocal lens safety and security cameras are generally much more pricey than repaired lens, however provide the complying with benefits. With a fixed lens, your installer would certainly need to physically move as well as re-install the cam to change the area of sight. With a varifocal lens, the installer can change the focal size to alter the area of sight.

Third Eye Installation Systems London for Beginners
We advise as well as make use of varifocal lenses for our installments as we can adjust the lens conveniently as well as they are typically much easier to function with. A CCTV cam iris functions in a comparable way to a still cam, the much more open the iris is, the brighter the photo will certainly be.